QtPass 1.7
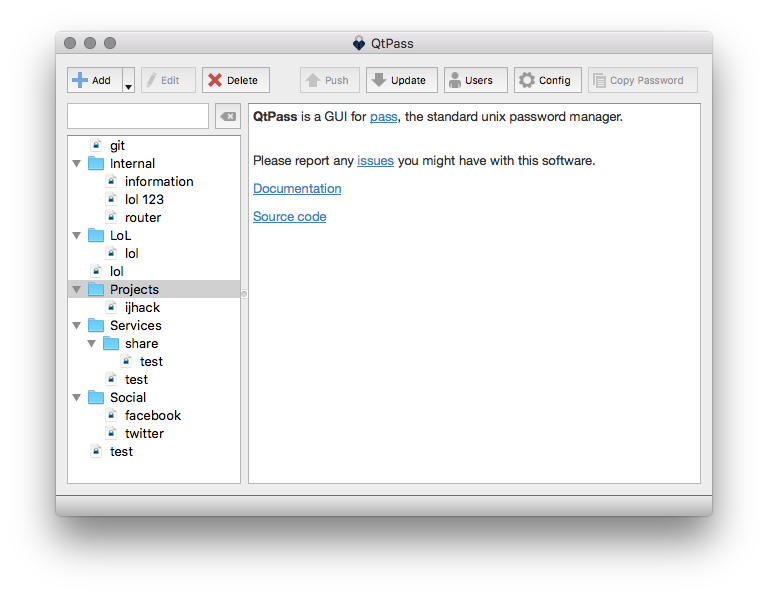
QtPass is a multi-platform GUI for pass, the standard unix password manager.
View the Project on GitHub IJHack/QtPass
v1.7.0
Highlights
- Spanish regional variants support (ES_AR, ES_EC, ES_MX, ES_UY)
- Qt 6.10 beginFilterChange/endFilterChange support
- Integration tests for core workflows
- Various bug fixes and code quality improvements
Bug Fixes
- Guard against out-of-bounds index in password character set
- WSL case-insensitive path handling improvements